PSP
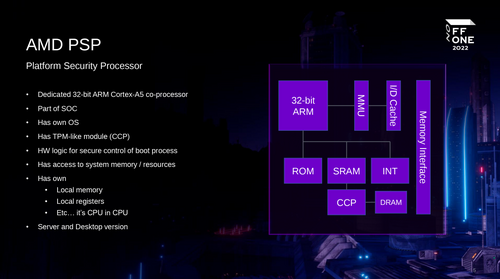
The AMD Platform Security Processor is a ARM Cortex-A5 with the TrustZone extention[1][2][3] that lives inside AMD CPU's since around ~2014 that is 16h and later.[4] The PSP is booted before the x86 CPU has started. It is believed that general exploit mitigation technologies (stack cookies, NX stack, ASLR) are not implemented in the PSP environment.[5]
reverse engineering efforts
- 2019 the AMD Platform Security Processorby Christian Werling and Robert Buhren
- Extracted PSP blob from Lenovo UEFI image - Details PSP "firmware filesystem", "directories" pointed to by the FET[6] and "second directories" pointed to by normal "directories" - These directories point to data or code (arm instructions)
- 2022 PSP UEFI Firmware Structure.pdf|AMD PSP UEFI Firmware Structureby George Zaitseff
- Collection of bios firmware ripe for extraction of PSP blobs[7] - Tools for extracting PSP blobs from firmware[8]
Vulnerabilities
- 2017 fTPM Remote Code Execution via crafted EK certificateby Cfir Cohen from google cloud security
- Host to PSP - Probably needs root?
- 2018 / RYZENFALL / CHIMERA[9] by CTS Labs
- Host to PSP and SMM - Persistent across bios and OS reinstallations - Privlage system access such as root requierd
- 2019 Platform DH key recovery via invalid curve attack (CVE-2019-9836)by fir Cohen from google cloud security
- Could be used to circumvent the memory encryption and leak sensitive data from SEV
todo
review following material and add sections accordingly https://media.ccc.de/v/thms-38-dissecting-the-amd-platform-security-processor https://media.ccc.de/v/31c3_-_6103_-_en_-_saal_2_-_201412272145_-_amd_x86_smu_firmware_analysis_-_rudolf_marek https://web.archive.org/web/20250313052559/https://dayzerosec.com/blog/2023/04/17/reversing-the-amd-secure-processor-psp.html https://github.com/dayzerosec/AMD-SP-Loader https://github.com/PSPReverse/PSPTool https://github.com/PSPReverse/PSPTrace https://danluu.com/cpu-bugs/
See also
https://en.wikipedia.org/wiki/AMD_PSP https://doc.coreboot.org/soc/amd/psp_integration.html
- ↑ https://en.wikipedia.org/wiki/AMD_PSP
- ↑ https://en.wikipedia.org/wiki/TrustZone
- ↑ https://en.wikipedia.org/wiki/Trusted_execution_environment
- ↑ https://freundschafter.com/amd-processors-without-amd-psp-secure-technology/
- ↑ https://seclists.org/fulldisclosure/2018/Jan/12
- ↑ https://github.com/eabase/UEFI-Repair-Guide-Wiki/blob/master/Terminology.md
- ↑ https://github.com/greg0r0/amd_psp_firmwares
- ↑ https://github.com/greg0r0/psp_uefi_dumper
- ↑ https://safefirmware.com/amdflaws_whitepaper.pdf